In financial history, 2017 may very well be noted as the year of the Initial Coin Offerings or ICOs. The year was hallmarked by hundreds of ICOs raising capital for utility tokens, most of which gave “usage rights” to a broad range of decentralized networks and products.
At the same time ICOs and token sales have proven a new category of venture investing and a new opportunity for startups to raise capital.
Realism has slowly entered the blockchain industry, as this hype has cooled down. While many continue to speculate on the “killer app of blockchain”, what if the first push to mass adoption is not a decentralized application, but the tokenized representation of something that already exists in the real world?
Security tokens constitute an investment contract of real world value, meaning that speculation over the token’s value concerns the underlying asset, not the token itself. This is a welcome relief from the utility tokens, where the value is extremely hard to assess. As we dig deeper into the possibilities of tokenizing securities, it becomes intriguing to what extent these digital assets can change the face of the financial industry.
In this article, we take a look at the definition and distinction of utility and security tokens and build our case as to why tokenized securities could in fact be a trillion-dollar opportunity that pushes blockchain technology into the financial mainstream.
The ICO craze
According to data provided by Fabric Ventures, a VC focussing on decentralized networks, and TokenData, an unaffiliated platform for tracking data on token sales, ICOs collectively managed to attract roughly $5.6 billion in investments during 2017. In comparison, “only” $1 billion was invested in blockchain projects by venture capitalists in the same year and in 2016, ICOs managed to attract a mere $240 million in funding.

Notable here is that the 10 biggest projects in terms of funding were responsible for 25% of all capital raised through ICOs in 2017.
Although the cryptocurrency market has been in a downtrend since early 2018, ICOs have still been pulling in billions, with the clear winners being EOS ($4 billion) and Telegram’s ICO ($1.7 billion). However, the continuation of the bear market has led to a strong decline in overall investments, yet another indicator of the highly speculative nature of the cryptocurrency space.
The reason is that no matter the excitement about these ideas and technology, very few utility tokens have unlocked real value thus far. In theory, decentralized networks have the potential to create strong efficiencies in time and costs, representing significant economic gains. However, we are yet to realize any of these efficiencies in the real world. It will take time before we can truly identify what industries, products and services blockchain-based solutions can and can’t disrupt and truly be able to assess the value of utility tokens.
The lion’s share of passed ICOs raised capital by issuing utility tokens, of which the function and future is not yet understood. However, as the narrative around utility tokens slowly shifts, a new type of token has emerged into prominence. This token finds itself on the crossroad of traditional finance and fintech and is backed by real world value: the security token.
Defining utility and security tokens
In the years leading 2018, entrepreneurs in the blockchain space were being very creative in their fundraising designs to prevent their token being regarded as a security, but as has become the standard in the industry, times are-a changing. The rapid increase in interest for tokenized securities attests to this dramatic shift in the industry and multiple sources touted 2018 as the “year of the security token”. Even though this has proven to be overly enthusiastic, the opportunities of security tokens are still very real, and still extremely early. But before we get to this, a clear definition and distinction of utility and security tokens is appropriate.
Utility tokens
Utility tokens represent access to a company’s (future) product or service — like a voucher. Utility tokens are not designed as investments, but as purchases. They are a unit of account for the network to which the utility token gives access, and the bigger the networks becomes, the more utility the token gives access to. Moreover, the utility token will become more valuable with an increase in demand as the industry standard is to cap the maximum number of issued tokens, which the majority of existing projects adhere to.
Participants of an ICO for a utility token are buyers of a product or service, not investors. The outcome of their purchase is the ability to use the product or service their utility token gives access to. Besides the access to the network, product or service, a utility token can also give access to dynamics such as the governance of the network and staking mechanisms, among many other features that can be coded in to the programmable digital assets.
To illustrate utility tokens in a real world context, we can compare these digital assets to pinball tokens. Such tokens provide access to one specific utility, playing pinball. Now imagine that there’s a limited number of these tokens and that the pinball game is continuously given new, valuable features in the form of new gameplay elements, making the pinball machine unique. The inserted tokens are distributed to those developing and adding value to the game, who can sell them to people eager to play. As more people want to play the game, the demand for the tokens will increase but the supply will remain the same, making the tokens more valuable. To illustrate the governance element of utility tokens, pinball token holders can use their holdings to vote on improvements to the game they want to see implied, and thus vote on which developer receives the tokens.
In conclusion, a defining characteristic of a utility token is that it is not designed as an investment, which exempts it from the extensive body of traditional security regulations.
Security tokens
Securities have been around since the 13th century and are widely understood and subject to extensive regulatory frameworks. Based onInvestopedia’s definition, traditional securities are financial instruments that hold some type of monetary value and represent ownership (stock), a creditor relationship (bond), or the representation of rights to ownership (option). They can provide a variety of financial rights to the owner of the securities, such as equity, dividends, or interest. Moreover, investors in securities expect the value of the security itself to appreciate over time.
Additionally, security tokens are defined as “essentially, digital and liquid contracts for fractions of any asset that already has value, like a house, a car or equity in a company”. Security tokens thus denominate fractional ownership of value-holding assets in tokens. A key difference with traditional securities is that security tokens represent programmable ownership, giving the assets more functionalities, flexibility and built-in automation of security-related processes.
Both securities and security tokens derive their value from their underlying asset and are generally very similar. Because of these similarities, security tokens are easily classified and subject to existing regulatory frameworks in place for traditional securities. Even though entrepreneurs in the space have been going through lengths not to have their token classified as a security to avoid to stringent red tape and high registration costs, having your token registered as a security does allow the digital asset to smoothly fit into existing rules and regulations. This enables the token to be compliant from the start instead of finding itself in the regulatory twilight most digital tokens are currently positioned in.
To illustrate the classification of a security, we can use the American Howey Test, a test designed to assess whether a transaction is in fact an investment contract. The test entails 4 core criteria:
- There is a capital investment;
- The investment is in a common enterprise;
- There is an expectation of profit;
- The profit stems from the work of the promoters or the third party (outside the investor’s control)
If these criteria are met, a token classifies as a security. However, questions have been arising as to whether the Howey Test and other security criteria, stemming from the pre-digital era, are still an appropriate measure for assessing whether an asset is a security, especially with the rise of security tokens. We’re expecting more legal clarity regarding this over the coming years.
Class confusion
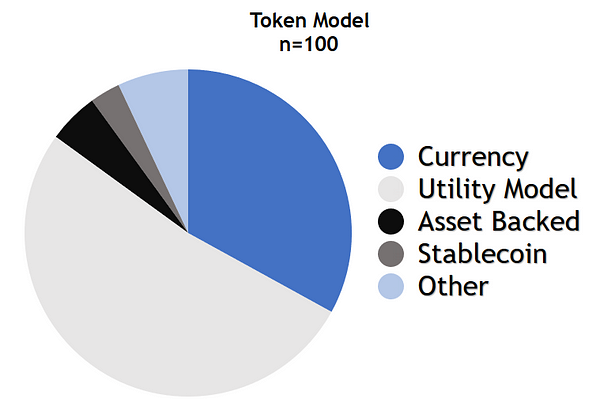
Up until today, utility tokens have been responsible for overwhelming majority of the total capital raised through ICOs and dominate the crypto industry. Based on this in-depth study of the token economics of the top 100 cryptocurrencies (up until April 2018), a little over 50% of the top 100 are utility tokens, followed by transactional cryptocurrencies such as Bitcoin, Monero and Nano, which model is responsible for 33%.
Another notable insight of this study is that it mentions that several of the utility tokens behave as securities, but as they are not legally classified as such, the researcher has categorized them as utility tokens.
A clear example of this is the recent decision of digital asset trading platform Iconomi to let their token holders exchange their previously labelled utility tokens for newly issued equity tokens. Reason given for this is the shift from a “total legal vacuum” two years ago to regulators zooming in on tokens that function like securities.
Both of these cases also shine light on the complexity of the classification issue, as since the dawn of digital tokens, authorities have been strugglingto establish the proper frameworks to legally categorize them. For example, Ethereum fit all the criteria of a security during its ICO, after which the asset slowly transformed into a utility token as it started to give access to more and more utilities.
The complexity of classifying these tokens is captured by common questions such as:
- Is buying a utility token an investment or a purchase?
- Is a decentralized network a common enterprise?
- Given that you become part of a decentralized network by buying and using the utility token of the network, aren’t you then contributing value (and thus creating profit) to the network just as the other participants?
- Who are the third parties generating profit in a decentralized network?
There aren’t clear answers to these questions and it is expected that the regulatory frameworks concerning utility tokens will be a mix between traditional regulations and new regulations, if there will ever be an all-encompassing regulatory framework for the continuously evolving programmable digital assets.
Utility tokens allow entrepreneurs to circumvent the stringent, yet necessary, regulatory frameworks in place for securities and raise capital from a global, non-accredited investor pool. However, utility tokens’ value is purely based on promises about highly experimental technologies, products and services that can only be fulfilled in the future, hence incorporate a lot of risk. Security tokens, on the other hand, represent a very tangible real-world value.
A trillion dollar opportunity
While the “security” classification of tokens has been created controversies in the industry, ironically, security tokens may represent the coming wave for the blockchain industry that finally push crypto assets to be adopted by the financial industry.
The strict regulations concerning securities that pose an initial obstacle could in fact be a blessing in disguise: they have the power to fully legitimize a token offering and ensure digital asset compliance from the beginning. The assets represented by security tokens have assessable value. Tokenized securities possess all the qualities of traditional securities, accompanied with a plethora of additional functionalities and benefits enabled by blockchain technology. They present a completely new way of organizing an industry that largely runs on outdated technology in a much more efficient manner than was possible before, functioning as the ideal bridge between the traditional security world and the blockchain industry. Traditional and crypto investors alike will understand security tokens.
The myriad of benefits presented by security tokens compared to the current security infrastructure include:
- Instant transaction settlement
- Lower fees due to the removal of non-vital middleman
- Fractionalization of assets (stocks, real estate)
- Increased liquidity and faster secondary market trading
- Immutable ownership, easily transferred
- Automated compliance
- Programmable functionalities (dividend payouts, voting rights, lock-up periods)
- Dramatic increase of addressable investor pool
- (Full) transparency, leaving less room for manipulation
- 24/7/365 trading
- Many more to-be discovered functionalities and dynamics as the industry matures
Taking these advantages into account, the multi-trillion dollar opportunity of tokenized securities becomes clear. They have the potential to open up otherwise inaccessible investment opportunities to investors around the world and can change the dynamics of securities for good. The technological upgrade to the security infrastructure alone could lead to desirable cost and time efficiencies, but the new functionalities enabled by blockchain technology is where the real opportunities lie. Tokenizing securities have already been touted as the biggest innovation in securities since the emergence of these assets and with $256 trillion in real world assetsglobally, calling them a trillion dollar opportunity might even be selling the rising phenomena short.
Regulatory Uncertainty and Sidelined Institutions: Barriers to STO Adoption
With global assets valued at over $250 trillion, and low hanging fruit of private equity and financial asset issuance valued in the tens of trillions, the opportunity of security tokens is immeasurably large. However, it is still early in the lifecycle of the STO, and there are several hurdles that stand in the way of security token adoption.
Securities are tightly regulated and for good reasons: they are there to protect investors from misinformation, manipulation and illegalities and ensure that security issuing companies are fully compliant. In current security infrastructure, these protections are guaranteed by middlemen that security token platforms aim to disintermediate. Therefore, it’s vital that these platforms incorporate the middleman services, such as underwriting, promotion, investor solicitation, insurance, regulatory compliance and institutional-grade levels of security, in the design of their platform, as well as provide regulated secondary trading platforms. This can be done through automated compliance protocols and additional supportive smart contract frameworks, however, the compliance of the platform still heavily depends on the cooperation of the jurisdiction such a platform operates in.

This need for a bridge between the vision behind security tokens and pragmatic regulation is at the core of LCX’s decision to base our headquarters in Liechtenstein. In the financial industry, Liechtenstein is known for its openness to innovation and this attitude is extending to cryptocurrencies and blockchain-based solutions. This has been underscored by the announcement of the Blockchain Act at the Finance Forum early 2018, an initiative aimed at providing legal clarity for organizations looking at implementing blockchain-based financial services.
The blockchain industry is innovating at an incredible pace, and it requires open-minded regulatory authorities who take action. Existing laws and regulations concerning securities will likely fall short when it comes to security tokens, as the programmability and unexplored nature of these digital assets presents novel challenges for compliance.
Moreover, while utility tokens were fuelled by retail investors, arguably, to unlock the true value of tokenized securities, institutional capital will need to enter the space. As we highlighted in our recent piece entitled “Institutions Sidelined: Why the Herd is Yet to Arrive”, this will only happen if the main concerns of these institutions are relieved. Regulatory uncertainty has been one of the main pain points for institutional capital and we are convinced that the welcoming approach of Liechtenstein’s regulators can greatly assist us in unlocking blockchain’s value-backed trillion dollar opportunity.
From network-backed to asset-backed tokens
Where utility tokens still have a long road ahead to legitimize their assigned valuations, security tokens will have a provable value from the day they are issued. Essential in this is regulatory compliance, which is one of the reasons why we at LCX are very optimistic about our choice to be in the heart of a jurisdiction at the frontiers of financial innovation.
The industry continues to mature. As the tale of the utility token remains unexplored and arguably uncertain, security token infrastructure is slowly being built. The coming wave of security tokens will represent a shift away from network-backed ideas, which have yet to become realities, toward assessable value grounded in legal rights and guarded by existing investor protections.
Will security tokens and the coming transition from network-backed utilities to asset-backed tokens take cryptoassets mainstream? This remains to be seen. What is clear, however, is that if successful, this opportunity is immeasurably bigger than we think.